The manufacturing industry is a vital part of the global economy, and its success is heavily reliant on an efficient supply chain. However, with the rise of industrial control systems (ICS) and connected devices, supply chain cybersecurity has become a critical issue for manufacturers, but what are ICS and Supply Chain Issues?
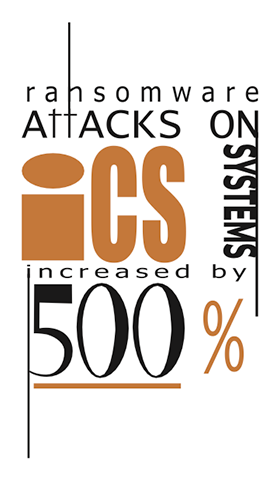
Industrial control systems (ICS) are computer-based systems used to monitor and control industrial processes. They are used in manufacturing to automate and optimize production processes, including assembly lines, chemical processing, and power generation. With the rise of the Industrial Internet of Things (IIoT), ICS systems have become more interconnected and more vulnerable to cyber threats.
Supply chain issues are another challenge facing manufacturers due to the fact that a disruption in the supply chain can lead to delays in production, increased costs, and a loss of revenue.
ICS and supply chain issues are intertwined because many manufacturers rely on ICS systems to manage their supply chains. For example, a manufacturer may use ICS systems to manage inventory levels, track shipments, and monitor production schedules; therefore, if an ICS system is compromised, it can disrupt the entire supply chain, leading to significant economic losses.
Challenges of Securing ICS and Supply Chain
Securing ICS and supply chain issues is challenging for several reasons. Firstly, many manufacturers have legacy ICS systems that were not designed with security in mind. These systems may not have the latest security patches or may be running on outdated operating systems that are no longer supported by the manufacturer.
Secondly, manufacturers often have complex supply chains involving multiple suppliers and contractors. Each of these suppliers may have their own ICS systems and security protocols, making it difficult to ensure that the entire supply chain is secure.
Solutions to Securing ICS and Supply Chain
To secure ICS and supply chain issues in the manufacturing industry, manufacturers need to take a multi-faceted approach by implementing the following:
Implement Security Best Practices: regular patching, vulnerability scanning, and user access controls. This can help to prevent common cyber attacks, such as phishing and malware infections.
Conduct Risk Assessments: identify potential vulnerabilities in their ICS systems and supply chains. This can help to prioritize security investments and ensure that the most critical systems are adequately protected.
Build a Cybersecurity Culture: Cybersecurity is not just the responsibility of IT departments. All employees should be aware of the risks and trained in best practices to prevent cyber attacks.
Monitor the Supply Chain: for potential cyber threats. This can include conducting security audits of suppliers and contractors, and implementing strict security requirements for all parties involved in the supply chain.
Utilize Advanced Security Solutions: such as intrusion detection systems, network segmentation, and threat intelligence, can help manufacturers to detect and respond to cyber attacks more effectively.
As ICS systems become more interconnected and supply chains become more complex, manufacturers need to take a proactive approach to securing their operations. By implementing security best practices, conducting risk assessments, building a cybersecurity culture, monitoring the supply chain, and utilizing advanced security solutions, manufacturers can reduce their cyber risk and protect their operations.
JD Young is a trusted Managed Network Services provider that specializes in helping manufacturing organizations tackle complex cybersecurity challenges. With their expertise in the industry, JD Young recognizes the criticality of ICS and supply chain issues facing manufacturers today. JD Young works with their clients to develop proactive security strategies that include risk assessments, security best practices, and building a cybersecurity culture. They also help monitor the supply chain to prevent vulnerabilities and threats from compromising the organization’s operations. Utilizing advanced security solutions, JD Young assists manufacturing companies to reduce their cyber risk and protect their operations, giving them peace of mind in the face of evolving cybersecurity threats.
We may not be able to solve all of life’s questions, but we can solve your technology needs.

